This article is about deploying Google Chrome extensions using Group Policy. Find out how to retrieve the extension ID and update URL.
Before reading this article, I recommend you to read the article Google Chrome on Citrix deep-dive to gain an in-depth understanding of all facets of Google Chrome for both Citrix and traditional environments.
Deploying Google Chrome extensions using Group Policy
A user can add extensions to the Chrome browser by downloading them from the Chrome Web Store:
This works great for individual users, but what if you want to deploy an extension to a large number of users in your organization? The solution is to deploy the extension via Group Policy.
Deploying extensions via Group Policy consists of two parts:
- Retrieve the extension ID and the update URL of the Chrome extension
- Enable and configure Chrome extensions in a Group Policy
Retrieve the extension ID and update URL of the Chrome extension
To be able to add an extension to a Group Policy, two values need to be known: the extension ID and an “update” URL. These two values must be entered as one string, but separated by a semicolon (;). For example, the concatenated string of the extension ID and update URL for the [recently retired] Microsoft Office Online extension version 1.5.2. is as follows:
ndjpnladcallmjemlbaebfadecfhkepb;https://clients2.google.com/service/update2/crx
The first thing to do is to manually install the extension directly from the Chrome Web Store on your (test) system. You need to do this, otherwise, you will not be able to retrieve the ID and update URL.
| Note: the URL of the Chrome extension also contains the extension’s ID, so technically speaking you could copy it directly from the browser’s address bar. Secondly, the update URL seems to be the same for all extensions, namely: https://clients2.google.com/service/update2/crx. What I am saying is that installing the extension on a (test) system is not necessary, but I still recommend it. At the very least, you will be able to test the extension before deploying it to your users and you can check if any additional settings (options) can be configured. You may want to inform your users about these additional options. |
The extension ID can be retrieved by opening the extensions tab in Chrome. Either enter chrome://extensions in the address bar or open the extensions tab via the menu:

Enable developer mode. Now the ID of each extension is shown.
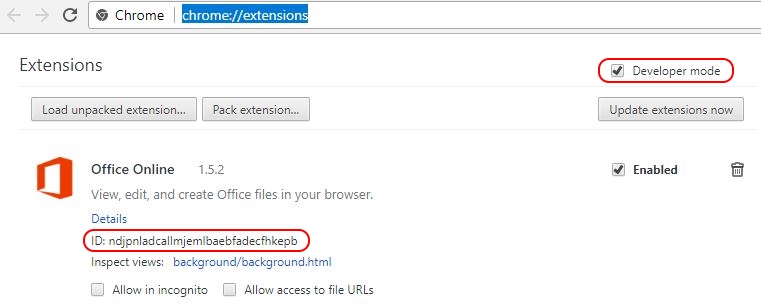
Copy this ID somewhere (for example in Notepad); you will need this information in the next step.
Chrome extensions are installed on a per-user basis. The installation directory is:
C:\Users\%UserName%\AppData\Local\Google\Chrome\User Data\Default\Extensions

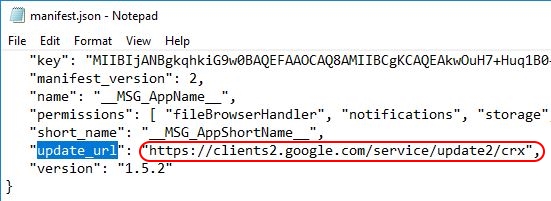
The extension ID is equal to the name of the folder. Open the directory that corresponds with the ID of your extension, in our case ndjpnladcallmjemlbaebfadecfhkepb (= the ID of the Office Online extension). Open the subdirectory representing the version of the extension. In the root of this directory, you should find the file manifest.json. Open this file in your favorite text editor (e.g. Notepad). Search for the string update_url. Here you will find the update URL:
Now you have the values you need. Copy them together in one string and make sure to separate them using a semicolon (as shown in the beginning of this paragraph):
ndjpnladcallmjemlbaebfadecfhkepb;https://clients2.google.com/service/update2/crx
In the following paragraph, you will enter this string in a Group Policy setting.
Configure the Group Policy setting to deploy the Chrome extension
Before you continue reading, please make sure that you have imported the Google Chrome ADMX files in your environment as described in the section Using Microsoft Group Policies (preferred) in the article Google Chrome on Citrix deep-dive.
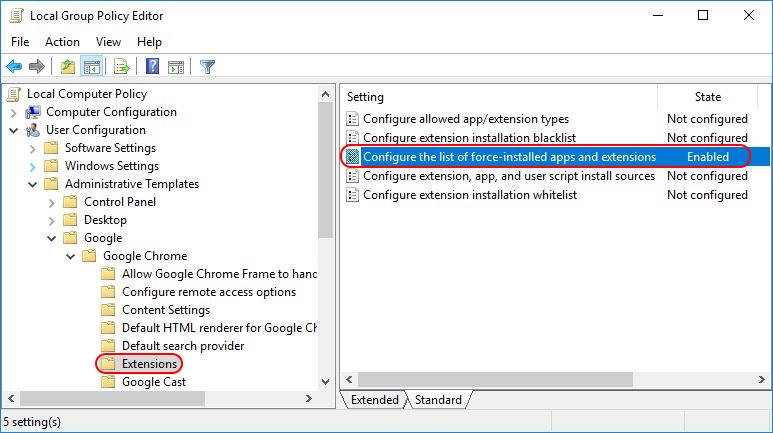
To force-install extensions, open your Group Policy Management console (gpmc.msc) and go to User Configuration \ Administrative Templates \ Google\ Google Chrome \ Extensions. Go to the setting Configure the list of force-installed apps and extensions and enable it.
Click the Show button and enter the string you created in the previous paragraph:
ndjpnladcallmjemlbaebfadecfhkepb;https://clients2.google.com/service/update2/crx
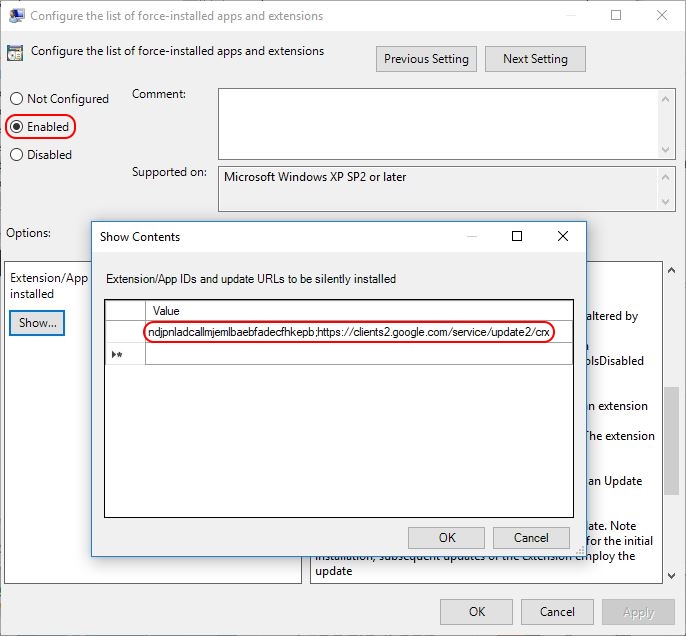
Now the policy setting is configured. On the next Group Policy refresh the user will automatically receive the required extension. To summarize, this policy will automatically install one or more extensions for all users to whom the Group Policy applies. The installation is executed silently and without user interaction.
As stated in the previous paragraph, after the extension has been installed you will find it in the directory C:\Users\%UserName%\AppData\Local\Google\Chrome\User Data\Default\Extensions.
| Note: make sure that developer mode is disabled on the extensions tab. During my tests, extensions were not automatically installed with developer mode enabled. |
Please be aware that when you remove the extension from the Configure the list of force-installed apps and extensions policy setting, the extension is automatically removed from Chrome for all users to whom the Group Policy applies.
Future updates of the extension are automatically installed through the update URL specified in the manifest file.
Unfortunately, I was not able to come up with a solution concerning the centralized management of Chrome extension settings. Some extensions come with additional options for the user to configure. As said, I was not able to find a way to manage or configure these centrally.
Dennis Span works as a Lead Account Technology Strategist at Cloud Software Group in Vienna, Austria. He holds multiple Citrix certifications (CCE-V). Dennis has been a Citrix Technology Advocate (CTA) since 2017 (+ one year as Citrix Technology Professional, CTP). Besides his interest in virtualization technologies and blogging, he loves spending time with his family as well as snowboarding, playing basketball and rowing. He is fluent in Dutch, English, German and Slovak and speaks some Spanish.

Pingback: Google Chrome on Citrix deep-dive - Dennis Span
For us it could be very useful!Great!
That’s great to hear Luca!
The ADMX files I downloaded on 3-Oct-2017, under Computer Configuration/Administrative Templates/Google/Google Update/Applications/Google Chrome, do not have the options you show. I only have:
Allow installation
Target version prefix override
Update policy override
I checked under all 53 nodes and not see the settings for Chrome Extensions. All 53 nodes have the same three settings listed above.
I see what the difference is. If you download just the ADM/ADMX bundle, you do not get all the admx files. You have to download the Chrome Bundle to get all the needed ADMX files.
The ADMX download is just google.admx and googleupdate.admx. The Chrome Bundle gives you:
chrome.admx
ChromeUSASwitcher.admx
google.admx
GoogleUpdate.admx
LegacyBrowserSupport.admx
PasswordAlert.admx
Hi Carl,
Nice to see you visiting my blog! 🙂 You are right, there is a difference in the downloads. Does it work for you now after you downloaded the Chrome Bundle?
Worked perfectly. Your instructions were crystal clear and easy to follow. I am working with a customer this morning who is having issues installing Chrome extensions for users on his XenApp servers. They will be pleased to see they do not have to alter the master image.
I will have to make sure their user profile solution is tracking the necessary folder.
BTW, I figured out my issue on the ADMX downloads. There are two links for “Download Chrome ADM/ADMX Templates”. The bottom one does NOT work. I clicked the “Download Google Update ADMX template” assuming that was what I needed. Obviously not. The top “Download Chrome ADM/ADMX Templates” link does work.
Thanks for your very clear and easy to understand and follow articles on the Chrome stuff.
Hi Carl. I am happy to hear that all went well and that the instructions were clear. I like the Chrome browser a lot, but the installation and configuration can be a bit tricky, especially in an enterprise environment and especially on Citrix hosted-shared or VDI. But I guess you realized that already. 😉
Very Good instructions.
Thank you for doing this.
Thanks Ray! You’re welcome. 🙂
i cannot find google in local group policy editor
Hi Koushik. Did you add the Google ADMX files to the local group policy central repository (C:\Windows\PolicyDefinitions) of that particular server? See also the section Using Microsoft Group Policies (preferred) in my article Google Chrome on Citrix deep-dive.
Thank you for the great tutorials. We have enforced couple of extensions for a group of users using com.google.chrome plist file. We have added “ExtesnionInstallForcelist” key with a value of “extensionID;https://clients2.google.com/service/update2/crx” with an always value. It has been working great except for one issue is that some of these extensions opens a welcome tab many times while the user is using Chrome. Do you have any clue how we can stop this? Thank you so much!
Hi Mona, unfortunately, I am no expert on MacOS. I do not know why the welcome messages appear. Perhaps you can contact the developer of the plugin directly. I think this would the best course of action. I am sorry I cannot be of more help to you.
Hi, I have pushed the GPO for pushing windows 10 accounts chrome extension as above. but it applies to only one system in the OU and fails for rest of the machines.
Hi Raghavva,
Do I understand it correctly that you assigned the policy to the machine? The Chrome extensions should be applied to the users, not machines. Also, the Chrome extensions are configured under User Configuration, not Computer Configuration. Please correct me if I misunderstood your comments.
Here’s a scenario I would like to do.. Have a GPO (lets call it ‘domain wide GPO’) deploying a chrome extension to every system in the domain. And then another GPO (accounting) applying to only a subset of computers in the domain. However, without doing anything special, all machines, including the accounting ones would receive the ‘domain wide GPO’. When the accounting machines refresh, they will get the ‘domain wide GPO’ as well as the ‘accounting’ one, but the domain wide one will win therefore ONLY applying the extensions set up in that. Is there a way to get the policies to ‘stack’ or ‘combine’ rather than having to create several GPOs with different lists of extensions applied to different sets of systems? And still have one that you can use to apply to ALL machines.
Hi Brian, my apologies for the late reply, but I was on holiday. First of all, Chrome extensions are not installed on the machine level. They are installed within the user profile (in the path “C:\Users\%UserName%\AppData\Local\Google\Chrome\User Data\Default\Extensions” to be exact). So you should use a user-based GPO and not a machine-based GPO. Secondly, in your example, the ‘accounting policy’ would win, not the domain wide GPO. And thirdly, I believe that the settings from both policies, when it comes to the list of extensions, are merged. I just did a quick with the Site to Zone Assignment list for Internet Explorer, which is also a “list based policy item” just like the one for Chrome extensions. I added different Trusted Sites to two policies; the Default Domain Policy and a lower-level policy on a child OU. The result was that my test user received a combined Trusted Site list consisting of both the list from the Default Domain Policy and the lower-level policy. So the lower level policy did not “win” or overwrite the Trusted Sites listed in the Default Domain Policy. So to answer your question and based on my quick test with the Site to Zone Assignment list, I would say that all extension settings from all policies will be applied to the user’s profile. Just make sure to test this before going into production.
Hi Brian,
Did you manage to find a solution for this? I have found that indeed, the Extension list is not additive when applying multiple gpos.
We have the exact same issue where only the accounting department should have the plugin for their banking tool, but there is a set of plugins to be deployed company-wide.
Regards,
Gert.
Hello. Faced the same problem. Has anyone managed to solve this??
Create a new GPO and copy all the company wide extensions and add the banking tool then scope the GPO to Accounting. This way only Accounting gets all company extensions and the banking extensions
B”H
Hi Dennis,
Please could you tell me if there is way to install a chrome extension in a closed internet environment where we do not have access to Google store ?
Thank you
Yechezkel
Hi Yechezkel, my apologies for the late reply. I was on holiday. Yes, it is possible to install an extension on a closed environment. This article describes the process accurately: https://blog.httpwatch.com/2017/11/15/installing-a-chrome-extension-without-an-internet-connection/. I tested it myself and it works. I do not know of any automated way how to install extensions offline though (I am not saying that it is not possible).
B”H
Hi Dennis, thank you for your reply. I need a way to install the extension automatically, the only method that I have seen so far is to build an internal IIS site and to put the extension on the site.
If you have a better idea I would be very grateful to hear from you.
Hi Yeckezkel, let me reach out to my contacts of the Chrome development team, ok? Perhaps they have a solution to automatically install the CRX file in an offline environment. I will contact you as soon as I have more information.
Hi Dennis,
I have tried configuring this policy for the offline setup where the vms do not have internet access. I have downloaded the crx file and put it in a share which is accessible from a Citrix server to which users will be connecting and accessing applications. I have configured the policy as below:
extn_id;\\sharepath\folder_having_crx_file
Is this the correct way of doing it? The policy is not working.
I apologize Govind, but I never tried to deploy non-public extensions. I am afraid I cannot be of much help in this case.
Hi Dennis,
I have i have developed a chrome extension (not available in chrome store). i followed the approach you provided but i see that extension is not deployed into my machine when using group policy.
i used text as efaidnbmnnnibpcajpcglclefindmkaj;https://clients2.google.com/service/update2/crx
Thanks
Hi Kiran, try the method described in the following article: https://blog.httpwatch.com/2017/11/15/installing-a-chrome-extension-without-an-internet-connection/. This should work. Bye, Dennis
Hello Dennis,
Great article and very intuitive. My only question is there any way of hosting this .crx file somewhere other than the webstore with a custom url?. My company has security concerns so we hosted privately. I followed instructions to the t but it will not work. Tell me if wont or maybe I’m doing something wrong?!
Thanks!!!
Hi Fausto,
Chrome does not support the type of implementation you are describing out of security reasons. It is possible to manually install a CRX file though. Please see this article: https://blog.httpwatch.com/2017/11/15/installing-a-chrome-extension-without-an-internet-connection/.
Really helpful article. Thank you Dennis. Now it would be great to know how to customize extension via GPO.
Hi Ivan. Thanks! Unfortunately, extensions cannot be customized using GPO, unless the developer of the extension would release an custom ADMX file for your Group Policies. So far I have never seen this.
I want to black list all extensions, which I have and add a whitelist.
The whitelist should be separated into two sections
Mandatory – Configure the list of force-installed apps and extensions
Subscribed – Whitelisted but not appear on Browser.
If i try to add some in the “Configured extension installation whitelist” and that did not work.
I then tried not configure the force-installed apps and extension and added them to the configured extnesion installation whitelist setting and that still didn’t work.
Deploying using GPedit.msc seems to don’t work anymore.
Instead: Use regedit.exe with https://www.chromium.org/administrators/policy-list-3#ExtensionInstallForcelist
Hi Konstantin,
Do you really mean the local “gpedit.msc”? In my article I never meant for anyone to deploy Chrome extensions using the local Group Policy editor “gpedit.msc”. Use the Group Policy console (“gpmc.msc”) instead.
Hi Deniss,
I Have deployed the chrome extension through GPO.Its successfully deployed but users are not able to enable,disable & remove is there any way to give them access to disable,enable or remove option from registry setting or through GPO.
Thanks,
Vaibhav
Hi Vaibhav,
No, this is not possible. The policy setting is also called “configure the list of force-installed apps and extensions”. One small possibility is to create an Active Directory group and deny this group the “apply policy” right on the specific group policy. This way, individual users can be added to this group and the policy would not apply to them, thus no extensions would be installed.
Hi Dennis,
Nice article. I am able to install extension present on web store. But I don’t want to publish extension to chrome web store and would like to host it on local store. I tried (for testing) pushed crx and update.xml file on google drive and added the path as mentioned in group policy editor. But changes are not reflecting. Can you please help on what I may be missing
Hi Yulu, someone else also once wrote a comment on this issue. In my answer I refer to an external website that may be of help to you.
Hi Dennis,
do you know a possibility to set the “allowed sites” inside the extension settings by group policy? We got an extension that we force install to our users but we also want to make sure that the extentions is only active at some whitelisted sites.
Hopy you can give us a hint. Thank you very much so far!
Sorry for the very late reply Max. So far I have never seen any possibilty to configure the actual options within an extension using Group Policy.
Great Article, But after placing below files into \\xxxx.xx\SYSVOL\xxxx.xx\Policies\PolicyDefinitions path. Google folder is not showing in gpmc.msc User administrative template.
chrome.admx
ChromeUASwitcher.admx
google.admx
GoogleUpdate.admx
LegacyBrowserSupport.admx
PasswordAlert.admx
am i going somewhere wrong?
Hi Monin. Did you also copy the .ADML files to the path \\xxxx.xx\SYSVOL\xxxx.xx\Policies\PolicyDefinitions\%Language% (e.g. \\xxxx.xx\SYSVOL\xxxx.xx\Policies\PolicyDefinitions\en-US)?
Hello Denis,
We are mass deploying an extension within our organization. The extension is provided by GPO and installs properly. My problem is that on some machines the extension is not enabled and since it is pushed by GPO the button is grayed out.
So, I’m looking for the registry key or file to modify to make the extension active for everyone.
Thank you
Thierry
Hi Thierry,
Please be aware that extensions are installed on a per-user basis and not per-machine. So if you want to assign the extension to all users you should use a policy that applies to all users.
I will leave my 2 cents and hope the formatting is not killing it. An example how we force to install Adblock. Hope it helps.
HKEY_CURRENT_USER\Software\Policies\Google\Chrome\ExtensionAllowedTypes\
1 = REG_SZ extension
HKEY_CURRENT_USER\Software\Policies\Google\Chrome\ExtensionInstallBlacklist\
1 = REG_SZ *
HKEY_CURRENT_USER\Software\Policies\Google\Chrome\ExtensionInstallSources\
1 = REG_SZ https://*.google.com/*/cfhdojbkjhnklbpkdaibdccddilifddb*
2 = REG_SZ https://*.google.com/*/iaiioopjkcekapmldfgbebdclcnpgnlo*
3 = REG_SZ https://*.google.com/*/fhbjgbiflinjbdggehcddcbncdddomop*
HKEY_CURRENT_USER\Software\Policies\Google\Chrome\ExtensionInstallWhitelist\
1 = REG_SZ cfhdojbkjhnklbpkdaibdccddilifddb
HKEY_CURRENT_USER\Software\Policies\Google\Chrome\ExtensionInstallForcelist\
1 = REG_SZ cfhdojbkjhnklbpkdaibdccddilifddb;https://clients2.google.com/service/update2/crx
Hi Dennis,
Thank you for the comment. This is the answer to my question.
Hello Dennis,
Thanks for the great info. It helped me setting up the pushing out an extension for our users. I initially set this up at user level and it did not get pushed out to all the users and then switched it to be at machine level and it appears to be now working.
The thing I still am unable to figure out is on how to update the settings for the extension through GPO. Did you find anything for it?
Thanks.
Hi, if you mean how to configure settings within a particular extension then I have to disappoint you. As far as I know, there is no way how to centrally manage extension settings.
This might be the sollution for us as well. GPO deployment just isn’t flexible enough yet.
Hello Dennis,
In our envi we have computer based GPO for chrome ext in place for all the member servers which is working fine but now we have to install another chrome ext only for few users. When i created user based based policy i can see registry entries are created for users but chrome ext is missing. I little confused whether computer based GPO is not allowing to execute User based GPO. In this case do we have any option to make this work please?
Hi, Chrome extensions are “installed” in the user’s profile. You have to use a user-based group policy. Which registry entries are you referring to? The Chrome extension does not create or modify any registry extensions. The group policy downloads and copies the extension’s files to the user’s profile and it modifies the user’s preferences file.
This string: [To force-install extensions, open your Group Policy Management console (dsa.msc)] should read
To force-install extensions, open your Group Policy Management console (GPMC.msc)
Oh, nice catch! You are right of course. I just corrected it. Thanks!
Hi Dennis,
I am happy to see your article about the Google Chrome Extension. I really need your help to resolve the chrome extension on environment.
1. I have enabled the “Configure the list of force-installed apps and extensions” setting and applied to users OU. (Enabled extension for PAWS tools value is: cecipmaogpgeicjemkdecdeimcopplji;https://clients2.google.com/service/update2/crx)
2. As you suggested, I have disabled the Developer Mode using the setting:
Control where Developer Tools can be used –> Enabled
Control where Developer Tools can be used –> Disallow usage of the Developer Tools
3. I am having the internet access on my desktop, but enabled extension not getting when user logged on the machine. I can see only “Symantec Extension” that is getting from the local policy.
4. I have raised the case with MS and they did not supported this issue, because it is a Google Chrome.
Could you please help me to resolve this issue?
Hi Sahayarajan. It seems that you did everything correctly. Developer Mode is disabled by default, so normally you would not need to configure a group policy setting. Just to make sure, the value you are using in your user-specific group policy is cecipmaogpgeicjemkdecdeimcopplji;https://clients2.google.com/service/update2/crx, right? That looks technically correct, assuming that the first part contains no accidental spelling mistakes. And you are sure that the group policy is actually applied to your user? Did you check using the command gpresult /r?
Thank you! This was a huge help!
Great to hear Chris! Thanks!
Hi Dennis,
Thanks for your tips !
I already use this solution to deploy the ClickOnce extension in the past and it was working as expected.
For information, i got a Citrix VAPPS farm with 4 client host (about 150 users).
Today i try to deploy a new extension that my customer need = Meta4 ClickOnce Launcher
I used the same policy as the previous extension and add a new line with the id and update url.
On 1 server i do a gupdate /force, wait a bit and open Chrome.
Here is my problem, the installation is not silent : a new tab open automatically on the extension page Meta4 ClickOnce and a download of the extension starts automatically and wait to be executed.
Do you have any idea how to make this totaly silent without any prompt for the finals users ?
Thanks by advance.
Julien,
Hi! I have never been able to find a way how to manage Chrome extensions other than getting them automatically installed. Perhaps you can contact the author directly.
This worked great. The extension I’m trying to push is installed but the user is getting an “Error” when they start Chrome. They have to click the ‘Error’ box in the upper right hand side of Chrome and and enable the extension. Do you know of anyway around this? It doesn’t behave the same way in Edge – that browser just automagically installs the extension without any user intervention.
I am not sure what causes the error. There may be a an issue with the local cache or the extension may be corrupted in some way. Does this happen to all users or just some? Although both Edge and Chrome are based on the Chromium engine and most extensions should work in both browsers, does the author state that the extension is supported on both browsers?
I was searching for adding toolbar in different sites but didnt get so much explained. Now, it is working… Thanks
Thank you for this – works perfect and publishes the Extension to the users Chrome profile easily – works in citrix environment with roaming Appdata also.
Question though; In the Adobe Acrobat extension options section the default action is to leave “Open PDFs in Acrobat” toggle turned off once it’s installed. Any way of forcing that on? Users can turn it on independently which tells me there must be somewhere we can force that on.
Thanks
Sorry for the late reply Nick. No, there is no way how to centrally configure options within an extension. Sorry.
hi and thank you for the article. It worked without a problem.
however, upon opening chrome the extension is disabled. Is there any way to automatically enable it?
thanks agian
Hi Tom, Chrome automatically disables extensions that are deemed unsafe. I do not have any other explanation as to why your extension would be disabled by default. Unfortunately, although deploying Chrome extensions via Group Policy is quite simple, there is no way how to centrally configure them.
Hello Dennis,
thank you for the great article!
Is it also possible to configure the flag “Allow access to file URLs” for the extension “Enable local file links” (ID nikfmfgobenbhmocjaaboihbeocackld) using GPO?
Best regards, Uwe
Hi Uwe, no this is unfortunately not possible.
This is super helpful article. I found that we can do the same way with Intune profile.
I’m still finding the way to apply pre-configuration for connection diaglog, and push it out to machines. Did you find anywhere or any how I can achieve this?
Thanks